Connect with Us
- GOT IT PROBLEMS?1300 765 911
- GET IN2TECH!REQUEST IT SUPPORT
We help your business Grow!
- Understanding MS Licenses: A Quick Guide for Your BusinessChoosing the right Microsoft license can streamline your operations and boost productivity.Here’s a brief overview of some popular options, including Shared Mailboxes, to help you decide what’s best for your business. Microsoft Exchange Online Plan 1Perfect for businesses needing robust email and calendar tools, Exchange Online Plan 1 offers 50 GB of mailbox storage per…
- How One Small Mistake Turned My Unifi Update Into a 3-Hour NightmareIf you’re updating the Unifi OS on your Cloud Key v1, **stop the operating system service first**! Doing so will save you from the same frustration I went through—trust me, it’s worth the extra 2 minutes. Now, here’s the full story of how a simple update turned into hours of troubleshooting. **The Setup** On Friday,…
- Being Cyber Stalked? You can do something.Ever received an email with an invoice attached that you know is bogus? Are you left wondering about what you can do about it? The Australian Government has a site set up for reporting Cyber attacks and scams, you can enter in a complaint online right here: https://www.acorn.gov.au/ – you can even report it anonymously…
- MS Office 365 Exchange Mailbox Creation FailsShared Mailbox Creation Fails This article deals with a Shared Mailboxes but the work around applies to a standard mailbox also. The Problem: When creating a shared mailbox with the same email address for a secondary domain, the process fails. For example, you have the two domains: firstdomain.com.au and seconddomain.com.au You have accounts@firstdomain.com.au and want…
- Hackers breach email steal thousands of dollars, are you protected?Aussie Hackers steal hundreds of thousands of dollars A spate of email attacks have reaped hackers hundreds of thousands of dollars when their house deposits were stolen due to compromised email accounts. How it happens Have you ever received an message stating your email account is compromised or over quota and then prompting you to…
- Logging into Office 365 Web Access Without Saving Credentials:Scenario: You have an Office 365 account, work or personal, licensed to you or your organisation. You also have need to occasionally log into Office 365 accounts to access Outlook. These maybe created for you by other organisations, to which you do not want their credentials saved on your computer as they may interfere with…
- Why artificial intelligence is needed in your security arsenal.1/12/2023 The Role of AI in Antivirus: Enhancing Cybersecurity In today’s interconnected digital landscape, cybersecurity is more critical than ever. As cyber threats continue to evolve, traditional antivirus solutions are no longer sufficient to protect against sophisticated attacks. Enter Artificial Intelligence (AI), a game-changer in the fight against malware, ransomware, and other malicious activities. 1. Understanding…
- Why Patch Management has to form part of your defensive IT strategy19/12/2023 Today, I want to share with you some insights on why Patch Management as a service (PMaaS) is important for your organization and how it can help you keep your systems secure and up to date. What is Patch Management as a service? Patch Management as a service is a cloud-based solution that automates…
- New ‘Bluekeep’ Windows vulnerability and how to protect your business from it.Microsoft Windows Security Vulnerability CVE-2019-0708, otherwise known as BlueKeep is the next major threat to computer systems around the world. The BlueKeep vulnerability is present in Microsoft’s legacy operating systems such as Windows 7, Windows Vista, Windows Millenium, Windows XP, Server 2003 and Server 2008 Rest assured if you are running on Microsoft Windows 10,…
- Logging into Office 365 Web Access Without Saving Credentials:Scenario: You have an Office 365 account, work or personal, licensed to you or your organisation. You also have need to occasionally log into Office 365 accounts to access Outlook. These maybe created for you by other organisations, to which you do not want their credentials saved on your computer as they may interfere with…
- Phishing Attacks and how to protect yourselfHow to protect yourself from phishing attacks What is phishing Phishing emails pretend to be from a trusted brand such as the ATO, the post office, larger retail stores etc. It’s a non-targeted attack sent out to a lot of people. The attackers know that a large percentage will fail but they only need a…
- How to add a MS Shared Mailbox account to your iPhoneShared mail boxes are part of MS Office 365’s Exchange email system and are a fantastic resource. They hold 50GB of email, is free of cost and can be assigned to one person or to multiple people in a team. The only stipulation is that you have to have an existing email license in order…
- Hackers breach email steal thousands of dollars, are you protected?Aussie Hackers steal hundreds of thousands of dollars A spate of email attacks have reaped hackers hundreds of thousands of dollars when victim’s house deposits were stolen due to compromised email accounts. How it happens Have you ever received an message stating your email account is compromised or over quota and then prompting you to…
- Is your Mac slowing down?It’s not unusual for a Mac or iMac to slow down after a few months or years of usage. Computers have always been prone to getting bloated and clogged up with both user files and programs, and the modern age of large disks and memory have just allowed us to store more and more without…
- How to share files from the IN2Tech Cloud Backup and Recovery system.Sometimes we need to send files or even folders that are larger than our email systems can cope with, if you are using our Online Backup and Recovery system then you can send a file or folder up to 2000MB in size! Here’s how… Open a web browser and logon to the following link with…
- Get rid of the Windows Lock Screen!Apart from the Windows Lock Screen being very nice to look at, it serves no purpose and adds a barrier to you logging in. If you’d like to get straight the logon screen and avoid the Lock Screen altogether, here’s how. Open the windows registry editor (regedit.exe) and…
- Windows 10 update reboots when you don’t want it to!If you’ve ever had the experience of Windows rebooting to install updates whilst you are trying to work then you know how frustrating it is. Thankfully there is something you can do to prevent this from happening. Click on Start, then the Settings Cog. This will open the Settings Window….
- Low Disk Space? Time for a Spring Clean!Your hard drive is full. You’re running low on disk space. You need more room on your computer. Whilst they may sound different, they are in fact all the same issue. You’ve been putting it off, working around it and just generally avoiding dealing with the issue. It’s time to clean up your hard drive….
- How to protect yourself from the WannaCry Virus!What is the WannaCryptor Virus? This past month, a new variant of the CryptoLocker virus was released into the wild and has already infected over 185,000 systems in 100 different countries. This particular strain is known as WannaCry, Wana Decrypt0r, WannaCryptor, or WCRY. As mentioned above, WannaCryptor is a new variant of the CryptoLocker virus. CryptoLocker viruses…
- How to select the right IT Company for your Business.How to find the right IT Support company for your business. Finding the right company to look after your IT needs is critical to ensure you get the service you require. The selection process can be hit and miss, so here is a quick guide on how to find the right support company for you….
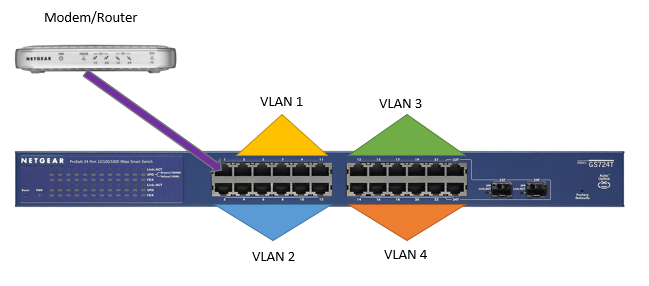
- Configuring Port VLAN’s on the Netgear GS724T Smart SwitchHow to setup a VLAN to share internet access whilst isolating the other VLAN’s. Documentation for specific setups is pretty scarce for Netgear so we are sharing a basic (but common) configuration from start to finish. Device: Netgear GS724Tv4 switch. Scenario: There is one internet connection via a standard Modem/Router combo device. There are four…
- My Computer is Slow! What Can I Do?So your computer has slowed down noticeably. Whether it’s all of a sudden or it’s been getting slower for a long time, you’ve decided that something needs to be done. Over the next couple of weeks, we’re going to go through some of the major cause s behind that sluggish behaviour. As always, if you have any…
- Online Backup over quota? Do a quick self audit!Are my backups over my limit? If you’re not sure if you’ve reached your backup quota, the first thing to do is to log into the Online Backup and Recovery Manager. This can normally be found on your desktop, but if not, a simple search from the start menu should bring it up. Once you’ve opened up…
- What to look for when buying a laptop or notebook for your businessWhat to look for when purchasing a Notebook for your business. Making a poor purchase with a new notebook will result in the unit costing you money over the long run in lost productivity and frustration. Unfortunately it’s easy to get taken in by the hype if you don’t know what you to look for….
- Why your new laptop is so slowWhy is my new laptop so slow? When purchasing a laptop, we’ve been conditioned to look at the central processing unit (CPU) and memory and that’s about it as far as the internals go. It’s always been bigger is better in regards to hard disk size, so as long as we have a decent CPU,…
- Windows update not workingAfter a new installation of Windows 7, Windows Update simply won’t work as it stalls during the check for updates. A bug in the Windows Update client is the cause and it’s triggered when there are a lot of updates to process. This is resolved by applying the KB3172605 update. However, installing this update can…
- No internet in Windows 10? Here’s a quick fix.We’ve had a number of clients in the last couple of weeks suddenly lose network connectivity for no apparent reason. After much troubleshooting we found a solution that has fixed this particular issue and takes just a few minutes and no technical expertise. Firstly, the issue: For the non technical…
- Multi-monitor systems in a business environment.How achievable is a multi-monitor system? Most users who have used dual monitor systems can’t imagine going back to a single screen as it does make your workflow much smoother.. Most PC’s and Notebooks can support dual screens out of the box, though you may need to purchase cables to suite. If you need to…
- Want to map a drive letter to your SharePoint library? Here’s how.IN2Tech Forum • View topic – Mapping O365 SharePoint Libraries in Windows 7 Access SharePoint Library’s like you do any other network folder. SharePoint is usually set up to synchronize to local computers via Microsoft OneDrive. We find that due to the regional locations or internet speed, that this process is frustrating our clients as…
- How to fix email bounce backs from legitimate email addresses.Non Delivery Report is received from a legitimate Email Address. If you are unable to send an email to an address that you know to be correct it may be due to the recipient moving to a new email provider. When you send an email to someone, MS Outlook stores the address in its ‘auto…
- How to protect your Business from Virus, Malware and theft.In the today’s world, a business succeeds or fails on its technology. We keep all our important information on computers so it makes sense to do everything we can to protect them from harm. In this Blog we’ll demystify the terminology and tell you how best to protect your critical IT assets. Anti-Malware and Anti-Virus Definition of…
- Security Alert – Bogus invoices in your emailEver received an email with an invoice attached that you know is bogus? Are you left wondering what you can do about it? Well there is something you can do! Firstly, right click on the email and then add it to your Junk Email block list. If you keep getting them then you can report…
- Does your business need IT support Melbourne?
 Our IT support services makes it easy for those non-techies to understand a problem and the solution we offer and implement.
As a business owner, you know it’s impossible to ignore the impact technology has on day-to-day life. We run though a few common reasons why business owners might need IT support.
If you need IT support in Melbourne, contact In2Tech – we’re here to help!
Our IT support services makes it easy for those non-techies to understand a problem and the solution we offer and implement.
As a business owner, you know it’s impossible to ignore the impact technology has on day-to-day life. We run though a few common reasons why business owners might need IT support.
If you need IT support in Melbourne, contact In2Tech – we’re here to help! - How Business IT Support Can Eliminate These Common Tech Mistakes
 It’s really no surprise to see how influential and integrated technology is.
In both our personal and professional lives, it’s hard to image a world without smartphones, notebooks, desktops, hard drives, and the cloud.
These days, technological change has a direct influence on a business, so if your business refuses to adapt, it wont be long before you’re left behind.
It’s really no surprise to see how influential and integrated technology is.
In both our personal and professional lives, it’s hard to image a world without smartphones, notebooks, desktops, hard drives, and the cloud.
These days, technological change has a direct influence on a business, so if your business refuses to adapt, it wont be long before you’re left behind.